A new one paper from Google Quantum AI has greatly reduced the estimated hardware needed to run the elliptic curve cryptography used by Bitcoin and much of Ethereum, bringing a long-running security debate closer to market terms.
At current market prices, quantum computing risks could affect more than $600 billion in Bitcoin, Ethereum, and stablecoins.
The paper, co-authored by Google researchers, Ethereum Foundation researcher Justin Drake, and Stanford cryptographer Dan Boneh, says that Shor’s algorithm for the 256-bit elliptic curve discrete logarithm problem can work with as few as 1,200 logical qubits and 90 million Toffoli gates or as few as 1,450 logical qubits and 70 million Toffoli gates.
Google says these circuits can be executed in a few minutes on a superconducting, cryptographically relevant quantum computer with fewer than 500,000 physical qubits, about a twentyfold reduction from previous estimates of the number of physical qubits.
Interestingly, Google does not say that such a machine exists today. Still, the Ethereum Foundation’s Drake said his confidence in a so-called Q-day in 2032 had risen sharply and that he now sees at least a 10% chance that a quantum computer could recover a secp256k1 private key from an exposed public key by then.
Meanwhile, Google combined the article with an unusual disclosure model, showing that it had been in contact with the US government and used a zero-knowledge proof so that outsiders could verify the resource estimates without receiving the underlying attack circuits.
The article says that advances in quantum computing have reached the point where fully publishing improved attack details has become less prudent, even as publishing reliable resource estimates remains necessary to motivate defenses.
Bitcoin’s problem is part race and part stock
For Bitcoin, the paper’s immediate market hook is timing. It models an “on-spend” attack in which a quantum machine derives a private key after a user reveals a public key by broadcasting a transaction, and then attempts to syndicate a competing transaction before the original payment is confirmed.
The paper says that a superconducting machine with a fast clock could reduce the live attack period to around 9 minutes from a prepared state, close to Bitcoin’s average block time of around 10 minutes.
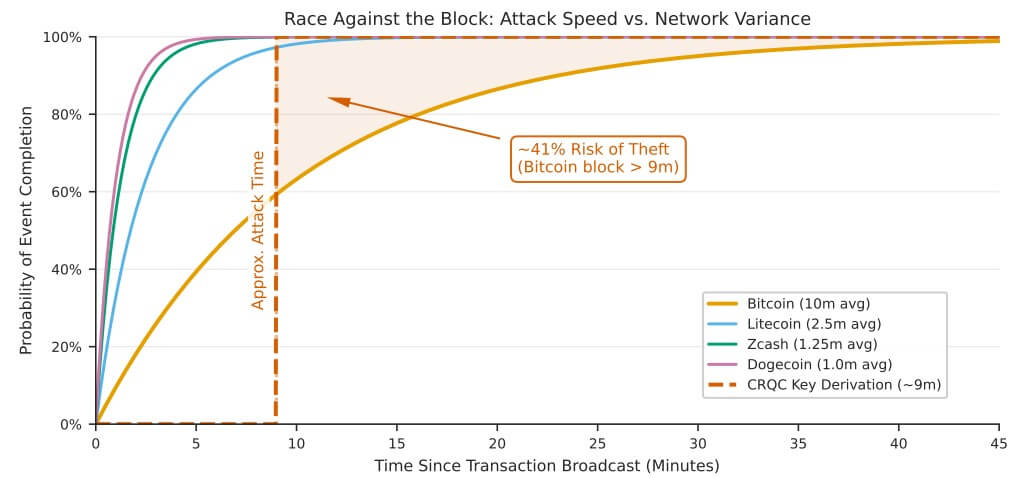
According to the article’s assumptions, this implies a probability of theft of just under 41%.
Meanwhile, that’s only part of the Bitcoin story, as the paper pointed out that around 6.7 million BTC are in vulnerable addresses. This equates to approximately $444 billion, or almost 32% of BTC’s total limit of 21 million coins.
Of these, the paper says that old Pay-to-Public-Key scripts still protect more than 1.7 million BTC, worth about $112.6 billion at the current market price, and that the total amount of dormant quantum-vulnerable Bitcoin could reach 2.3 million BTC across all script types, or about $152.3 billion.
These coins cannot all be migrated by simply asking current users to transfer money, as many are believed to have been abandoned, lost, or otherwise inactive.
Apart from that, the authors also claim that despite the privacy and flexibility benefits, Taproot has re-introduced a quantum weakness as Pay-to-Taproot puts the custom public key directly into the lock script.
They added that Grover-based attacks on Bitcoin mining will remain impractical for decades, leaving the short-term focus on signatures rather than proof of work.
That leaves Bitcoin with two different problems. One is the risk of live trades if a future high-speed machine can reliably break keys within the settlement window. The other is a large supply of older or exposed coins that could become regular targets in a post-CRQC world.
The article explicitly states that every existing Bitcoin transaction type is vulnerable to on-spend attacks from a future fast-clock machine, while older P2PK outputs and modern P2TR outputs introduce their own exposure at rest.
Ethereum’s quantum risk runs through wallets, validators and tokenized assets
Meanwhile, quantum risks for Ethereum are presented differently.
The paper says it’s unlikely that early, fast quantum computers will launch the same kind of on-spend attack there, because Ethereum produces blocks in deterministic 12-second time slots, processes most transactions in less than a minute, and already relies heavily on private mempools.
Instead, the main quantum threat lies in idle attacks on long-lived accounts and their associated systems.
The paper estimates that a fast attacker could crack the thousand highest net worth Ethereum accounts, containing approximately 20.5 million ETH, in less than nine days. At Tuesday’s ETH price of approximately $2,023.46, that equates to approximately $41.5 billion.
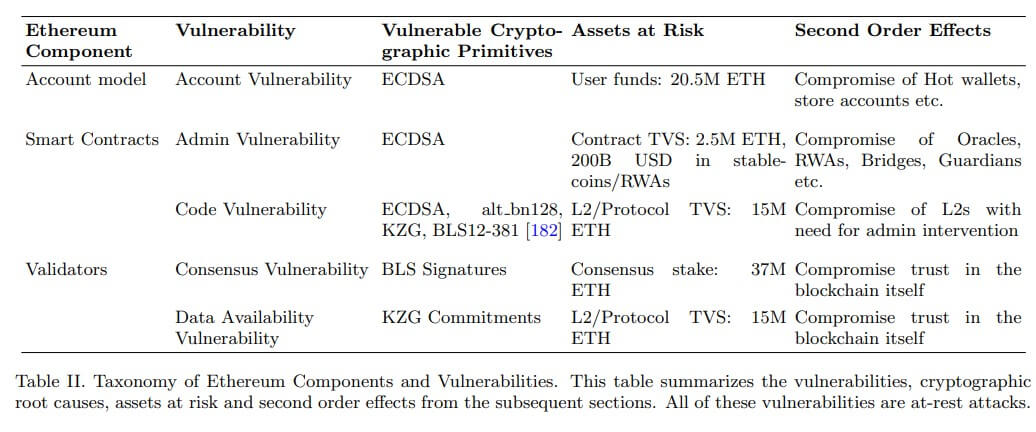
Among the top 500 contract accounts by ETH balance, the report says that at least 70 accounts holding approximately 2.5 million ETH are exposed via administrative keys, a bucket worth approximately $5.1 billion at current prices, with a private-key diversion attack on those accounts taking less than 15 hours on a fast clock machine.
Meanwhile, the larger institutional story lies behind these equilibria. The article links custodian vulnerability to approximately $200 billion worth of stablecoins and tokenized real-world assets on Ethereum and says these keys can function as control points for issuers, bridges, oracle operators, and emergency guardians.
The paper warned that a successful quantum attack on such accounts could enable arbitrary minting, fake rate feeds, frozen user funds or drained liquidity pools, depending on the system. The article says this is why standard asset balance models underestimate the true value of risk.
The lens is then further magnified. In the Ethereum risk taxonomy, the document flags approximately 15 million ETH in Layer 2 and protocol value exposed through code vulnerabilities and data availability, equivalent to approximately $30.4 billion at current prices, and approximately 37 million ETH in consensus interest exposed through BLS signature-related risks, or approximately $74.9 billion.
These numbers overlap with other components of Ethereum’s architecture, but together they show why the article treats Ethereum as a broader infrastructure problem rather than a story about wallet security.
The pressure shifts from theory to migration
Against this backdrop, the industry continues to wonder whether blockchains, wallets, exchanges and issuers of tokenized assets can migrate before the economics of the attack change.
Charles Guillemet, the Chief Technology Officer (CTO) at Ledger, said:
“The good news is that we already have the tools: Post Quantum Cryptography, now we need to migrate.”
However, the Google article says the process will take years, and the industry cannot wait for perfect clarity on the exact arrival date of cryptographically relevant quantum computers.
According to the company, this requires both protocol work and changes in wallet behavior, including reducing exposure to public keys and ending key reuse where possible.
Essentially, vulnerable cryptocurrency communities need to transition to post-quantum cryptography without delay.
For Bitcoin, this means a race against a settlement window that no longer seems comfortably wide. For Ethereum, this means protecting not just coins, but the much larger pile of contracts and tokenized claims that now rest on the same fragile math.



