Stablecoin issuer Circle is facing mounting criticism from blockchain researchers after millions of USD Coin (USDC) were stolen and flowed unhindered through its own bridge during its $285 million operation of the Solana-based Drift Protocol.
The inaction during the April 1 attack, which is now the largest decentralized finance (DeFi) hack of 2026, stands in stark contrast to Circle’s aggressive asset freeze tied to a sealed US civil case just days earlier.
This juxtaposition has reignited debate over the responsibilities and inconsistencies of centralized stablecoin issuers operating in permissionless markets.
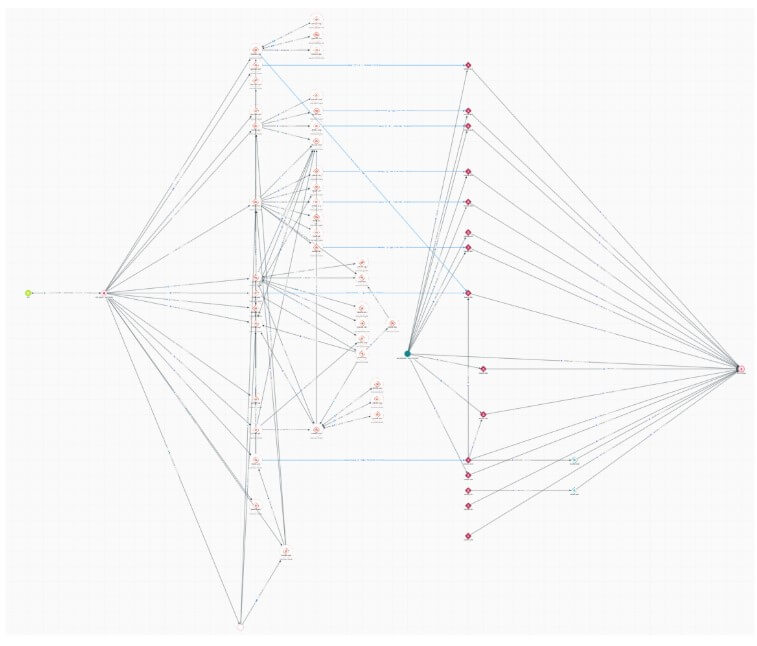
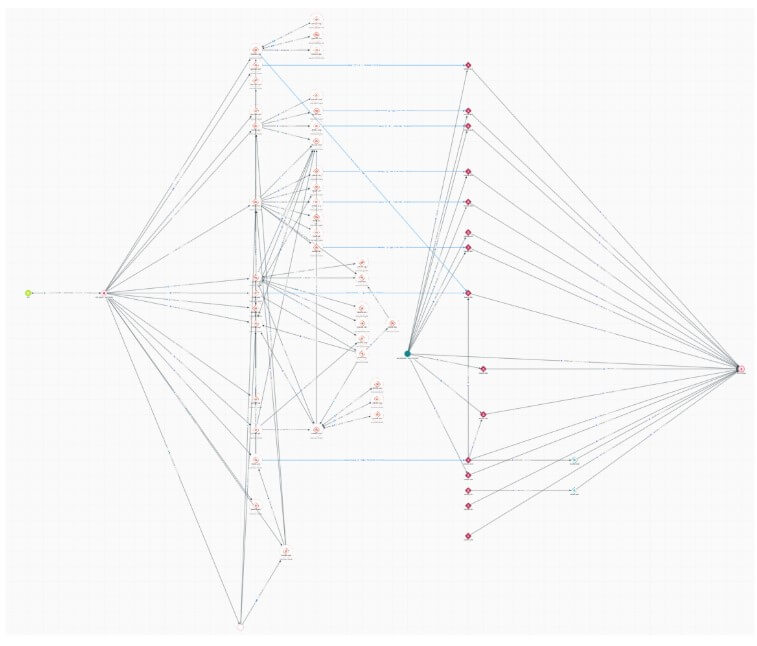
According to on-chain researcher ZachXBT, the attackers transferred more than $230 million in USDC from Solana to Ethereum via more than 100 transactions using Circle’s Cross-Chain Transfer Protocol (CCTP).
Why this is important: The episode highlights a structural tension in crypto markets: stablecoins like USDC operate within permissionless systems but maintain centralized control. When that control is applied inconsistently, it introduces new risks for users, protocols and regulators trying to understand where to intervene and where not to intervene during a crisis.
The transfers took place over several hours during the US business day, giving the New York-headquartered issuer ample time to act.
This view was confirmed by other security experts, who noted that the attacker held stolen USDC in multiple wallets for one to three hours before switching to Ethereum.
The hacker notably avoided converting the funds to Tether’s USDT, which suggested a calculated bet that Circle would not stake its authority on the smart contract blacklist.
That bet paid off because USDT is the largest stablecoin by market cap, and its issuer is known for blacklisting malicious attackers who use its assets to move money.
The bourgeois contrast
The timing of the exploit has amplified the backlash. On March 23, Circle froze the USDC balances of 16 unrelated business hot wallets and disrupted legitimate exchanges, casinos and payment processors in response to a civil dispute.
ZachXBT previously characterized that action as “potentially the most incompetent” freeze he had witnessed in five years.
Critics are now asking a fundamental question: If Circle claims the power to freeze assets to force compliance, why does it aggressively wield that power against legitimate companies while ignoring a confirmed, nine-figure heist ripping through its own infrastructure?
However, Santisa, the pseudonymous CIO of investment firm Lucidity Cap, argued the opposite. He declared:
“Circle not blacklisting is actually quite cypherpunk of them, regardless of the reason. The industry pushing for active blacklisting is taking us further and further away from decentralization – not necessarily a bad thing! Just a trade-off.”
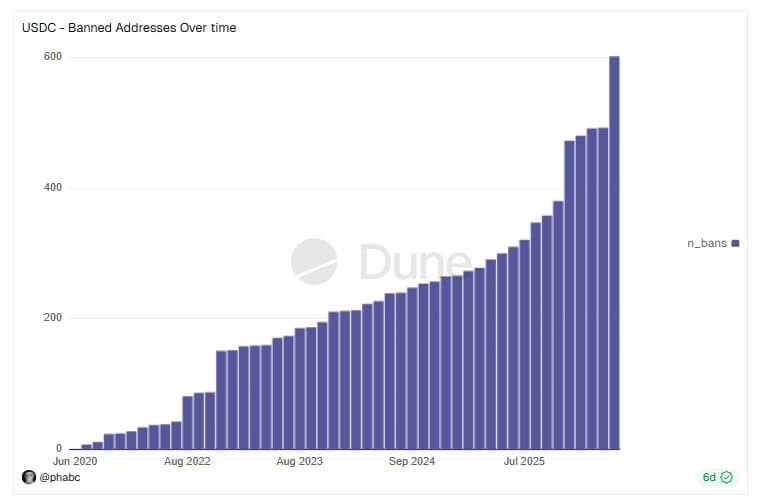
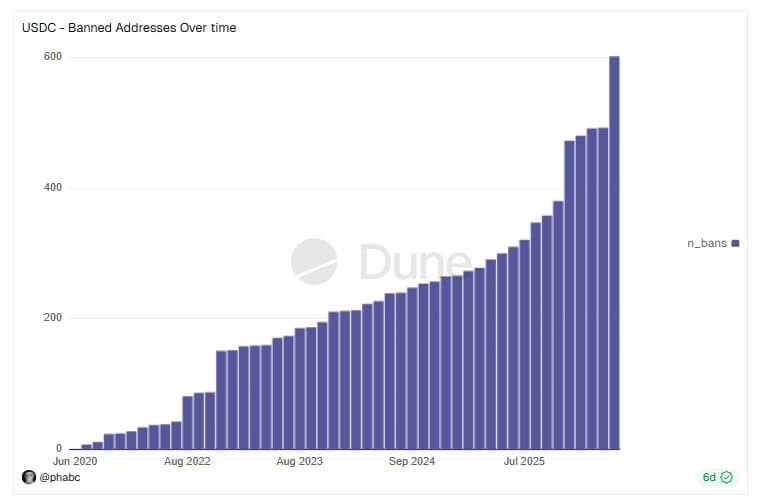
To date, Circle has blacklisted approximately $117 million across 601 wallets, according to Dune Analytics factswhich shows that the possibility exists.
Anatomy of the Drift exploit
The attack on Drift, previously the cornerstone of Solana’s DeFi ecosystem with over $550 million in Total Value Locked (TVL), was a highly sophisticated operation that lasted weeks.
According to the Drift Protocol post-mortemthe attackers endangered the Protocol’s Security Council.
On March 30, they used a mechanism known as a “Durable Nonce” to quietly obtain the necessary multisig approvals.
The durable nonce is a tool designed to keep unconfirmed transactions valid indefinitely for offline approvals. Yu Xian, the founder of blockchain security company Slowmist, said:
“Another encounter with the durable exploit of the noce offline pre-signature mechanism. This phishing technique has been prevalent for at least two years. Once such a signature has been phished away, the attacker can initiate ‘legally signed’ on-chain operations at a future convenient time – for example, in the Drift scenario this resulted in the takeover of his on-chain administrator rights.”
On April 1, the attackers changed the administrative authority, initialized a fake asset called CVT, artificially increased its value through oracle manipulation, and borrowed against the fake collateral.
In a short time, they emptied the vaults of JLP Delta Neutral, SOL Super Staking and BTC Super Staking. DefiLlama data shows that Drift’s TVL collapsed to less than $250 million after the attack.
The fallout has quickly spread across the Solana DeFi ecosystem, given Drift’s prominent role.
According to reports, at least 20 third-party applications that relied on Drift’s vaults to generate revenue have had a confirmed financial impact, including Prime Numbers Fi, which estimates losses at more than $10 million.
Who is behind the attack?
Although the identity of the attackers remains unknown at the time of writing, Drift says declared on X that it had found critical information about the parties involved in the exploit.
Meanwhile, security experts have noted that the sophisticated money laundering method points to a known adversary of North Korean attackers.
Blockchain intelligence firm Elliptic reported that the behavior in the chain and the indicators at network level are consistent with the operations of the Democratic People’s Republic of Korea (DPRK).
Another blockchain security company, Diverg, goes further declared:
“We, together with TRM Labs and Elliptic, can confirm that North Korea’s Lazarus Group (TraderTraitor) [was behind the Drift attac]. [The] same unit [was] behind the $1.5 billion hack of Bybit [and] Ronin’s $625 million attack.”
If confirmed, the Drift exploit would mark the eighteenth North Korea-linked crypto theft this year, pushing the regime’s illicit loot past $300 million by 2026.
It comes amid an escalation of state-sponsored attacks targeting crypto infrastructure, including a recent software supply chain compromise attributed by Google to North Korean threat actor UNC1069.



