Google’s Threat Intelligence Group (GTIG) warns that a “new and powerful” iOS exploit kit, dubbed Coruna by its developers, has been deployed on fake finance and crypto websites designed to lure iPhone users to pages that can silently deliver exploits. For crypto holders, the risk is blunt: GTIG’s analysis shows the campaigns ultimately focused on collecting seed phrases and wallet data from popular mobile apps.
Coruna targets Apple devices running iOS 13.0 through iOS 17.2.1 and bundles five full exploit chains and 23 exploits. GTIG says it recovered the kit after tracking its evolution through 2025, from early use by a commercial surveillance company customer to “watering hole” attacks on compromised Ukrainian websites, and eventually to large-scale distribution through Chinese-language scam sites linked to a financially motivated actor it tracks as UNC6691.
A crypto lure designed for iPhones
In the scam wave phase, GTIG says it observed the JavaScript framework behind Coruna being deployed on a “very large set” of fake Chinese websites largely focused around finance. One example cited by GTIG is a fake WEEX-branded crypto exchange page that tried to push visitors to an iOS device, after which a hidden iFrame would be injected to deliver the exploit kit “regardless of their geolocation.”
Related reading
The delivery mechanisms matter because they blur the line between traditional phishing and outright device compromise: according to GTIG, simply arriving at the booby-trapped page from a vulnerable iPhone was enough to start the chain. The framework fingerprints the device to identify the model and iOS version, then loads the appropriate WebKit exploit for remote code execution and a pointer authentication (PAC) bypass.
GTIG linked one WebKit RCE which it patched to CVE-2024-23222, noting that it was addressed by Apple in iOS 17.3 on January 22, 2024.
At the end of the chain, GTIG says Coruna is dropping a stager it calls PlasmaLoader (tracked as PLASMAGRID) and describes it as focused less on classic surveillance functions and more on stealing financial information. According to GTIG, the payload can decode QR codes from images stored on the device and scan text blobs for BIP39 word strings, along with keywords such as “backup phrase” and “bank account,” including in Apple Memos, which it can then exfiltrate.
Related reading
The cargo is also modular. GTIG says it can retrieve and run additional modules remotely, and that many of the modules identified are designed to connect functions and exfiltrate sensitive information from common crypto wallet apps, including MetaMask, Trust Wallet, Uniswap’s wallet, Phantom, Exodus and TON ecosystem wallets such as Tonkeeper.
The wider arc was also highlighted by mobile security company iVerify, which published its own findings around the same time as GTIG’s report. “And that’s exactly what happened here, but on mobile devices. Phone OEMs are doing as well as anyone can…”
What Crypto Users Can Do Now
Google says Coruna is “ineffective against the latest version of iOS” and urges users to update. If updating is not possible, GTIG recommends enabling Apple’s Lockdown Mode. GTIG also says it has added the identified websites and domains to Google Safe Browsing to help reduce further exposure.
For crypto-native users, the immediate takeaway is practical: mobile wallets sit at the intersection of valuable assets and high-frequency web traffic, making visit-to-compromise campaigns uniquely dangerous. GTIG’s reporting shows that the scam funnel wasn’t just about getting victims to connect wallets, but getting them onto the right device and iOS version so exploitation could do the rest.
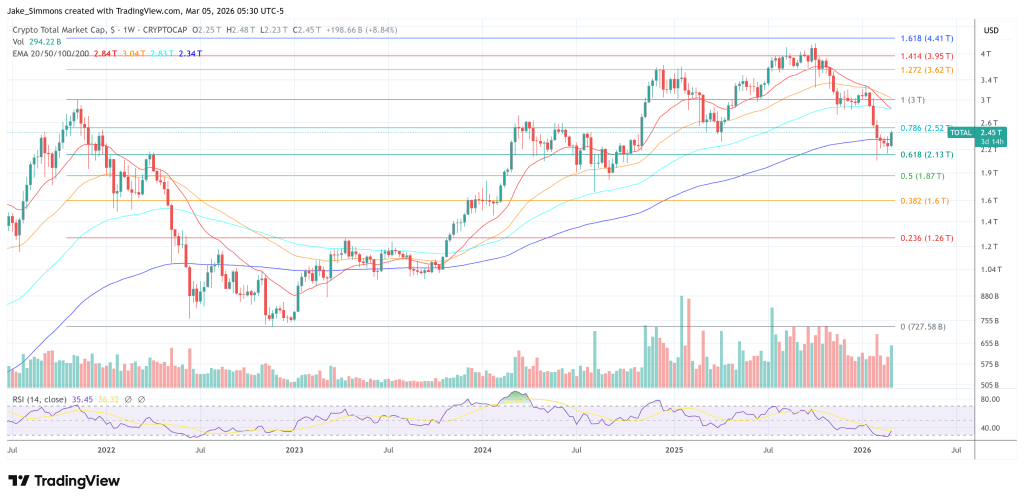
At the time of writing, the total crypto market capitalization was $2.45 trillion.
Featured image created with DALL.E, chart from TradingView.com

