- Hackers who posed while the staff exploited NFT projects and stealing nearly $ 1 million.
- North Korean linked groups are behind 70% of the crypto-thefts in 2025, including the $ 1.5 billion Bybit-Hack.
A new wave of Crypto -exploits has turned the web 3 space upside down, because Hackers occur that the staff has successfully infiltrated several NFT collections to Pepe -Makmaker Matt Furie and left with almost $ 1 million in stolen assets.
Attacked web3 projects and losing suffered
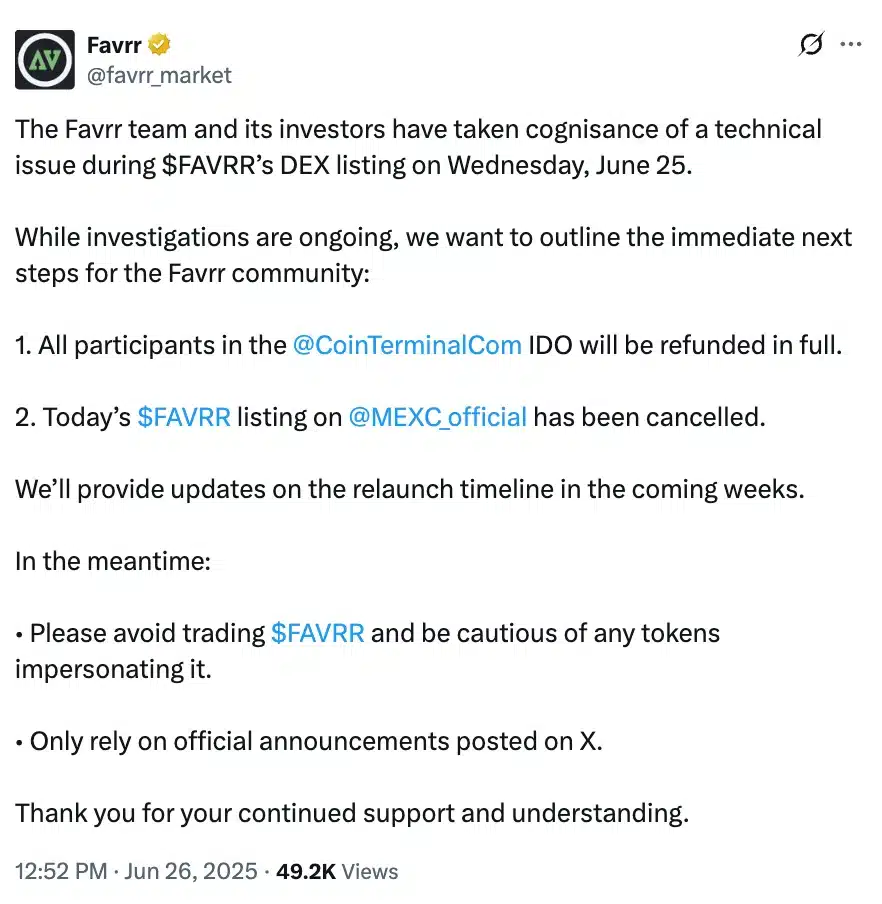
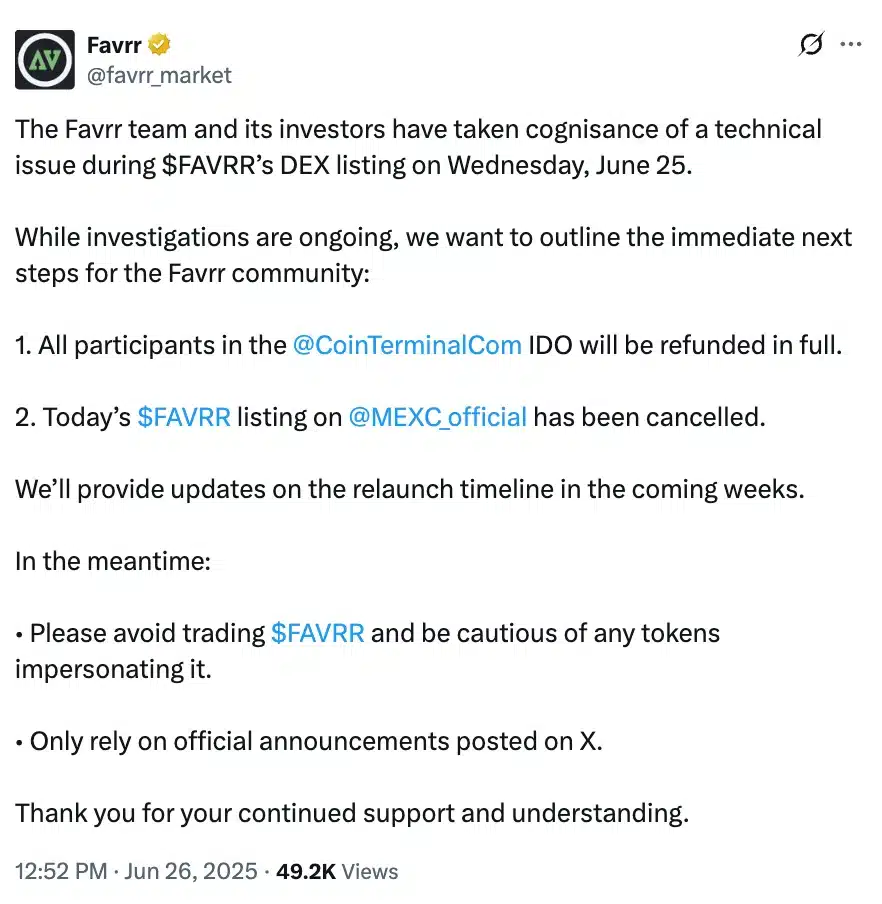
According to analyst on-chain ZackxbtThese attackers had Insider access to projects such as Favrr, Replyandy and Chainsaw, among other things by posing as legitimate technical employees.
Source: Zachxbt/X
Once within manipulated, they manipulated the NFT coin systems to generate large batches tokens, loaded to scale and caused a collapse of the market value.
The exploit not only ended funds, but also destabilized the affected ecosystems, which exposed serious vulnerabilities to internal access control and project security.
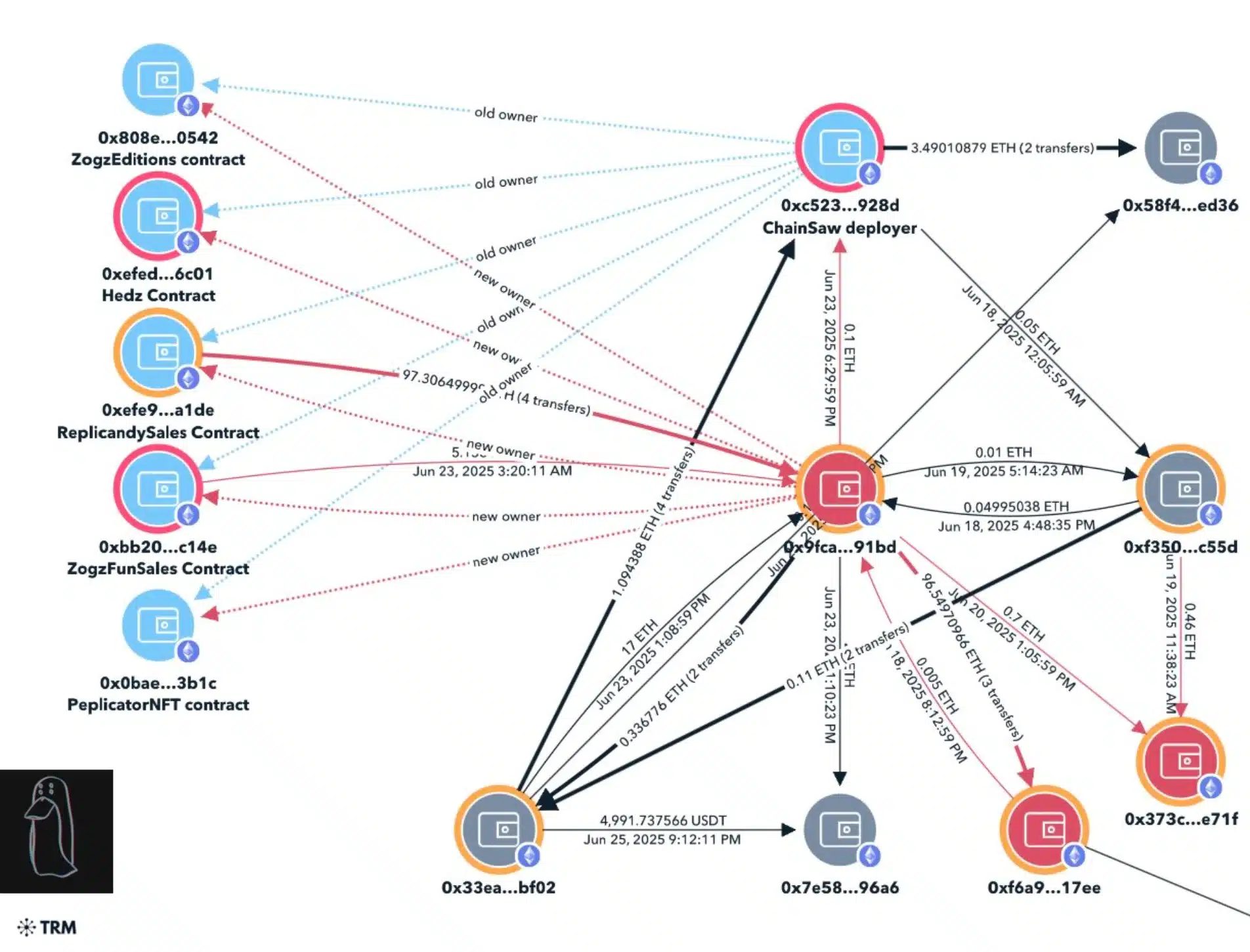
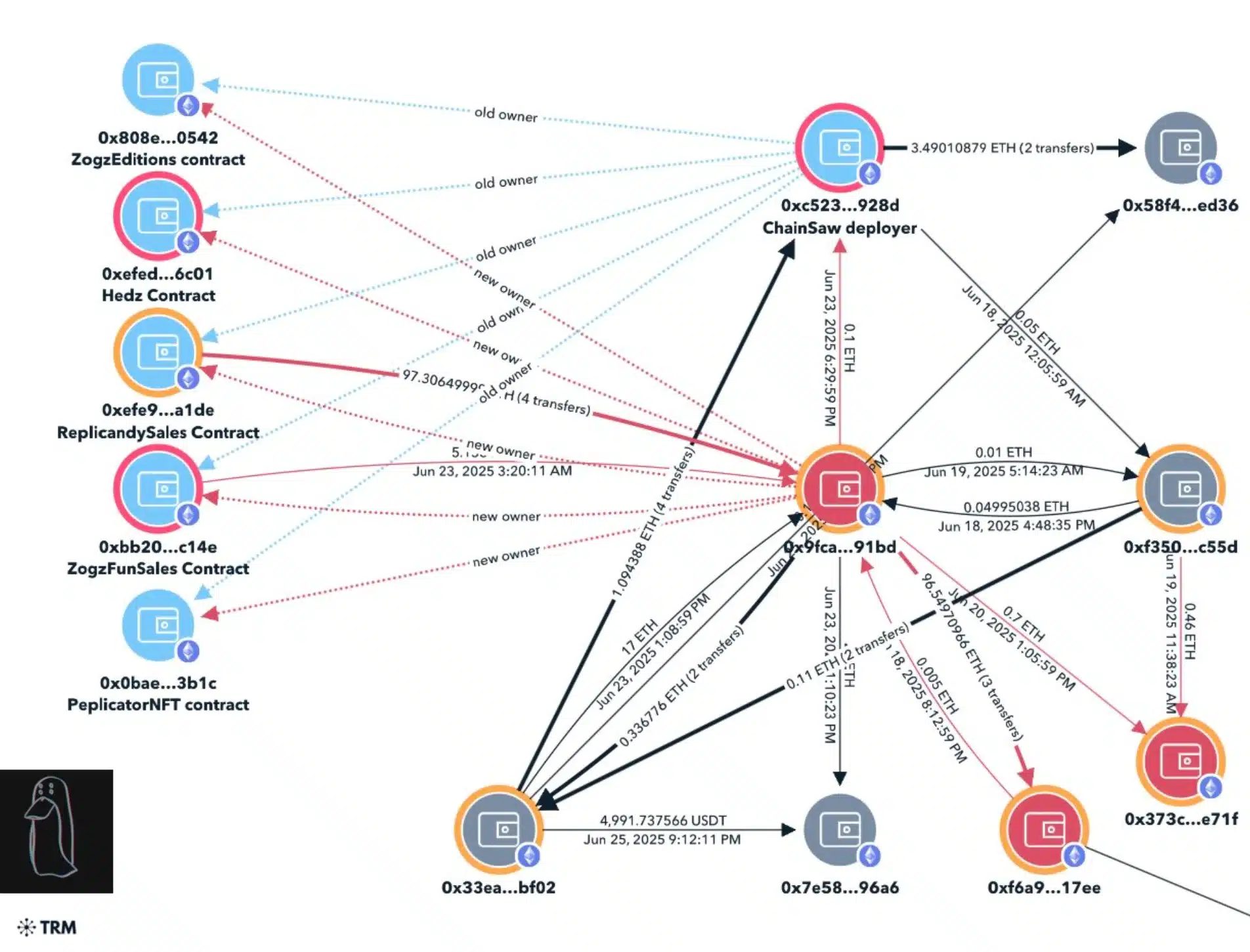
The timeline of the Replicandy exploit reveals a methodically executed infringement, with strong indicators that link it to North Korean IT agents.
How was the hack performed?
On June 18, the ownership of the Replicandy contract was quietly transferred to a new address (0x9fca), which later attracted coin revenues and resumed the mining, eventually crashed the floor price by overflowing the market with NFTs.
Source: Zachxbt/X
This pattern was again repeated on June 23 with extra collections, peplicator, Hedz and Zogz, causing further devaluation and losses of a total of more than $ 310,000.
Analysis on the chain followed the stolen funds via multiple portfolios, in which ultimately USDT deposits were uncovered to Mexc and two suspicious Github developer accounts identified ‘Devmad119’ and ‘Sujitb2114’, linked to the violation.
Internal logs have further exposed inconsistencies, such as developers who claim to be in the US during the use of Korean language institutions, time zones of Asia/Russia and astral VPNs.
These red flags strongly suggest that the attackers were part of a coordinated North Korean campaign that exploits lax control procedures in hiring web3.
While the Favrr team responded quickly with improved measures for users’ safety, chainsaw only gave a short warning and removed it later.
Source: Favrr/X
On the other hand, Matt Furie remained completely silent and hinted that the broader image indicates a much more disturbing reality.
The rise of North Korean hackers
That said, hackers linked in North Korea in 2025 became increasingly aggressive, with researchers attributing more than $ 1.6 billion this year, about 70% of all stolen crypto, attributing to groups affiliated by the state.
The stunning Bybit of $ 1.5 billion infringement In February, now considered their work, is the greatest crypto -theft in history.
These actors, including the notorious Ruby Sleet Group, have extended their reach outside of crypto, previously infiltrated about American defense contractors and now aimed at IT companies through fake rental campaigns and extensive social engineering tactics.
In response to the growing wave of crypto-related fraud and infringements of security, countries steps all over the world guarantees regulatory guarantees.
In the United States, Trump administration actively promotes a series of pro-Crypto policy that is designed to protect the industry against discriminatory bank practices and excessive regulatory pressure.
These include a pending executive order to prohibit financial institutions to focus on crypto companies, efforts to return sec-laid down restrictions such as SAB 121 and legislative support for frameworks such as the Genius Act to clarify rules for stablecoins and digital assets.
In the meantime, Australia has quickly moved to tackle the abuse of crypto-atm by taking cash transactions on AU $ 5,000, enforcing stricter identity controls and requiring real-time scam warning.
Together, these measures reflect a coordinated international shift to a safer and responsible web3 environment.

